Attribute-Based Access Control (ABAC)
Attribute-Based Access Control (ABAC) is a dynamic and context-aware access control model that grants or denies user access to user journeys based on attributes associated with users and their context.
Unlike traditional access control models like Role-Based Access Control (RBAC), which rely on predefined roles, ABAC evaluates policies at runtime using user profile attributes and authentication context to make fine-grained access decisions.
In ReachFive, ABAC allows you to control who can enter a user journey (signup, login, or access to an application) and what rights are granted once access is allowed Coming soon.
ABAC is evaluated during authentication and relies primarily on user profile attributes, such as verified identifiers, custom fields, or roles defined on the user profile.
These attributes can include:
-
User profile attributes (for example, verified email, country, custom fields)
-
User roles or classifications (for example,
staff,senior_staff,admin)You can create these using Custom fields.
-
Authentication context (for example, login method or assurance level)
ABAC policies are evaluated dynamically and consistently across all user access points.
ABAC flow

At a high level per Rule Type:
-
A user attempts to access a public journey (
signuporlogin). -
ReachFive evaluates ABAC rules using user profile attributes.
-
If rules match, access is blocked.
-
If rules do not match, authentication completes.
-
Coming soon Access token claims are issued based on user attributes.
-
A user attempts to access a public journey (
signuporlogin). -
ReachFive evaluates ABAC rules using user profile attributes.
-
If rules match, authentication completes.
-
If rules do not match, access is blocked.
-
Coming soon Access token claims are issued based on user attributes.
ABAC layers in ReachFive
ABAC in ReachFive operates at two complementary layers.
Layer 1: Controlling access to user journeys
The first layer controls whether a user is allowed to enter a user journey, such as signup or login.
At this stage, ReachFive evaluates user profile attributes against access rules before completing authentication.
Examples:
-
Block login attempts using unverified identifiers.
-
Prevent access if required attributes are met or not met depending on Rule Type.
-
Restrict login based on user classification or status.
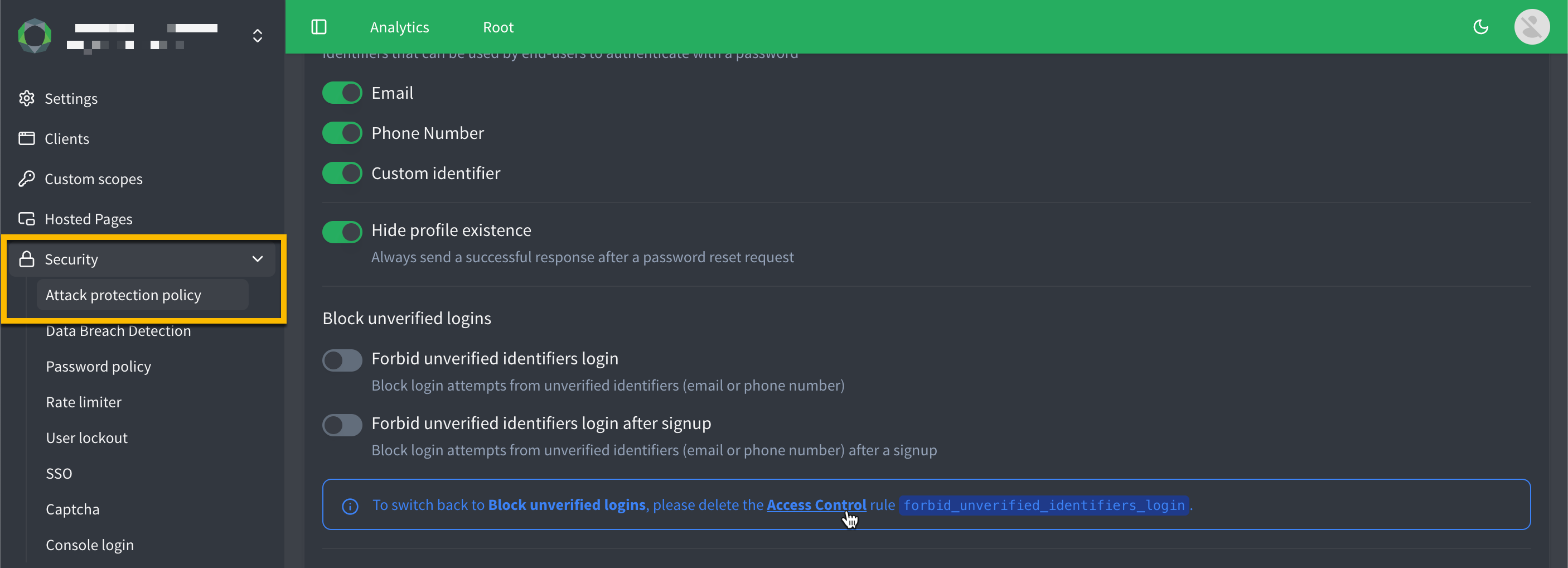
This layer expands existing security capabilities, such as Forbid unverified identifiers login, which is now managed as part of Access Control rather than Attack Protection.
Layer 2: Granting personalized access after authentication
Coming soon
Once a user is authenticated, ABAC can enrich the access token with claims derived from user attributes.
These claims allow applications to enforce authorization decisions downstream.
| As of 2026-05-28, this layer is currently still in development and not yet available in the ReachFive Console. |
Examples:
-
Grant access to different portals based on user role.
-
Enable or disable features based on custom attributes.
-
Apply business-specific authorization logic.
Applications can inspect access token claims to determine whether a user is allowed to proceed.
ABAC and access tokens
When ABAC policies are applied successfully, ReachFive can include selected attributes or roles directly in the access token.
For example:
-
A
roleclaim indicating the user’s role -
Custom claims derived from user profile attributes
Applications can then evaluate these claims:
-
If
role = senior_staff, allow access -
Otherwise, block or redirect the user
This approach keeps authorization logic simple and consistent across applications.
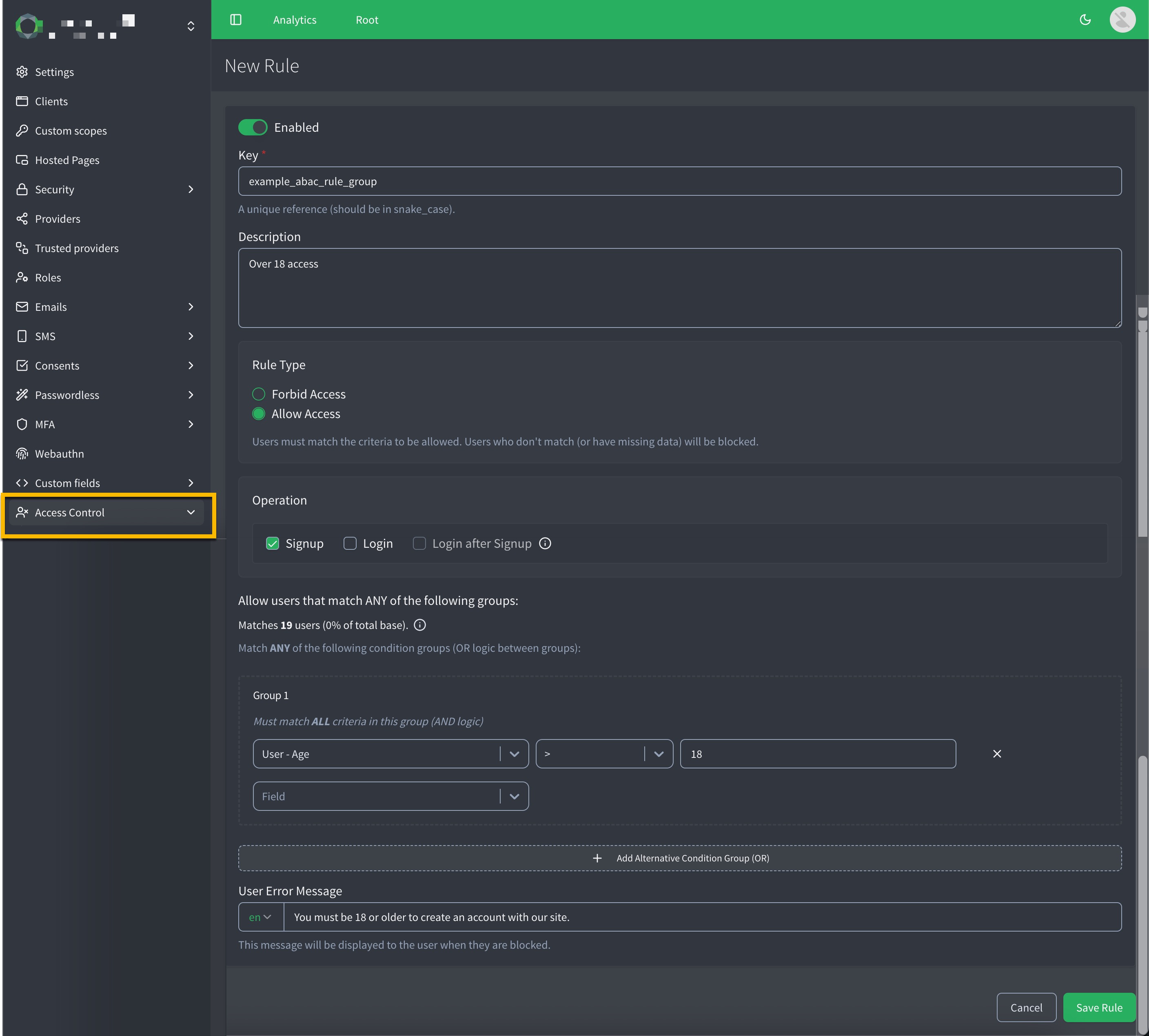
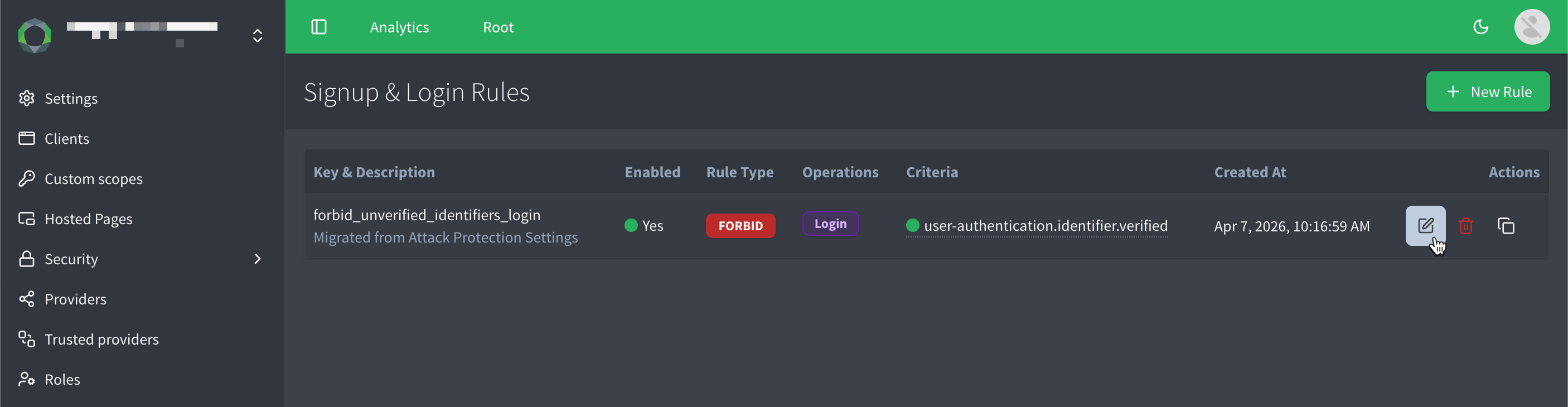
Create ABAC rules in the ReachFive Console
Attributes used by ABAC are defined and managed directly from the ReachFive Console. Once defined, these attributes can be referenced in ABAC rules.

You create rule groups where multiple attributes are evaluated together to determine if a user can authenticate or not.
-
The attributes within a group use
ANDlogic, meaning all attributes must match for the user to match the group criteria. -
The attributes between groups use
ORlogic, meaning if a user matches any group, they will be denied access.
When creating a group, the console dynamically updates how many of your users match the currently selected criteria.
To create a new rule in the ReachFive Console:
-
Go to .
-
Click New Rule.
-
Define the Key (snake_case).
-
Give the rule a Description.
-
Select the Rule Type.
-
Forbid Access
-
Allow Access
-
-
Select Forbid all for one or more of the following:
-
Signup
-
Login
-
Login after Signup
-
-
Define the attributes and values to evaluate for this rule group.
Repeat this for additional groups.
-
Define a User Error Message to display when access is denied.
This is a user friendly message that explains why access was blocked and what the user can do to resolve it (if applicable).
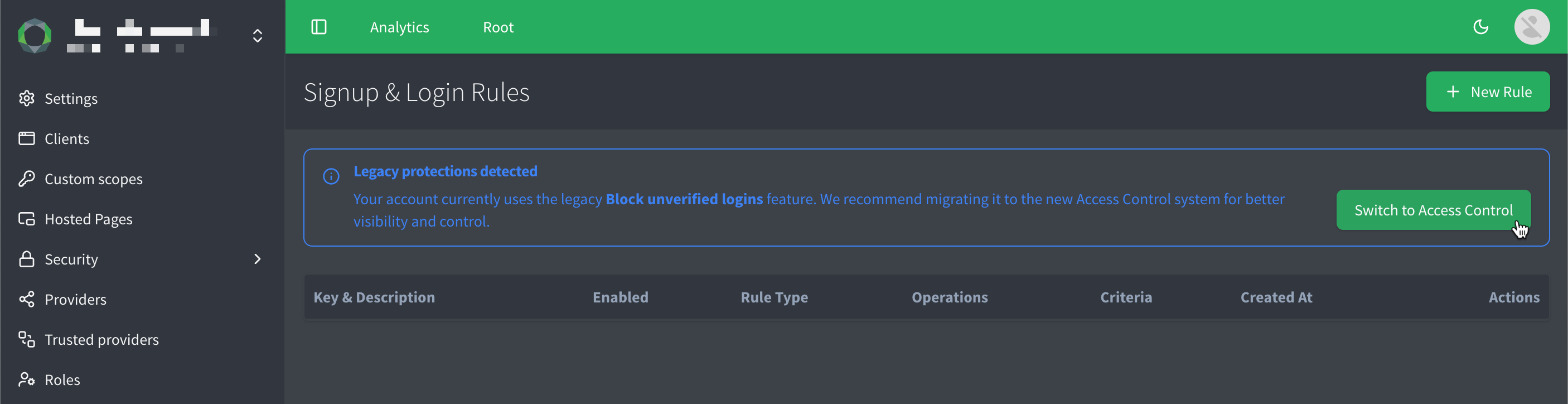
Migrate to Access Control
If you were previously using the the legacy Block unverified login attempts feature, you’ll see the option in the Attribute-Based Access Control (ABAC) section of the ReachFive Console to automatically migrate your existing block on unverified logins configuration to an equivalent ABAC rule.
Migration process:
-
Click Switch to Access Control in the ABAC section of the ReachFive Console if prompted.
-
A dialog appears letting you know that your existing block on unverified logins configuration will be converted into an ABAC rule. It also informs you of API error format changes that are required if you were previously relying on the old error response for unverified logins.
The error changes from
error.unverifiedLogintoerror.accessControl.login.forbidden.Click Proceed to migrate to Access Control.
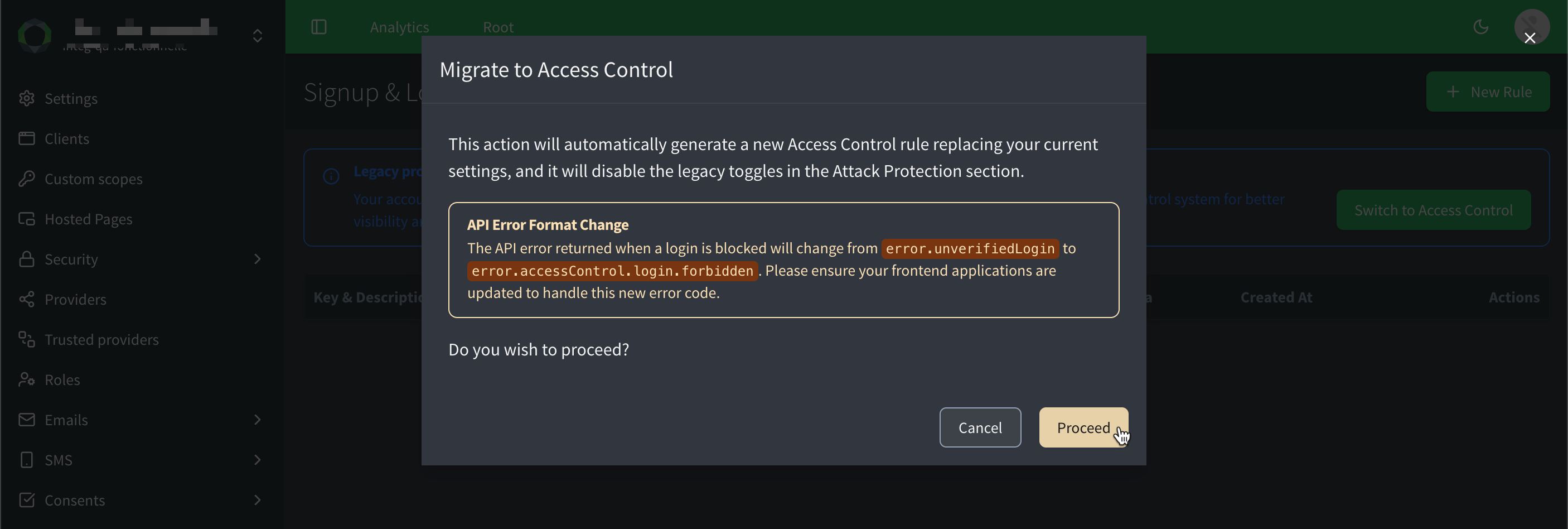
-
And voila! Your existing configuration is now an ABAC rule, and you can further customize it as needed.
Downgrade to legacy block on unverified logins
If you find that Access Control does not meet your needs, you can choose to downgrade back to the legacy block on unverified logins feature.
To downgrade back to the legacy block on unverified logins, you must first delete any ABAC rules that were created during the migration process, as well as any additional rules you may have created after migration.
Once all ABAC rules have been deleted, the option to downgrade will become available in the ReachFive Console.