14 August 2025 (v2.140)
ReachFive v2.140 introduces several improvements and needed bug fixes.
Here are some new features and notable updates:
As always, we fixed a few items for you.
Configurable MFA session expiry
You can now configure how long the MFA AMR scope remains valid in the MFA settings section of the ReachFive Console. Set the session lifetime anywhere between 1-720 hours (default: 72 hours).
The MFA session resets after a strong authentication; for example, after re-entering a password plus OTP, or completing a step-up operation like approving a high-value purchase.
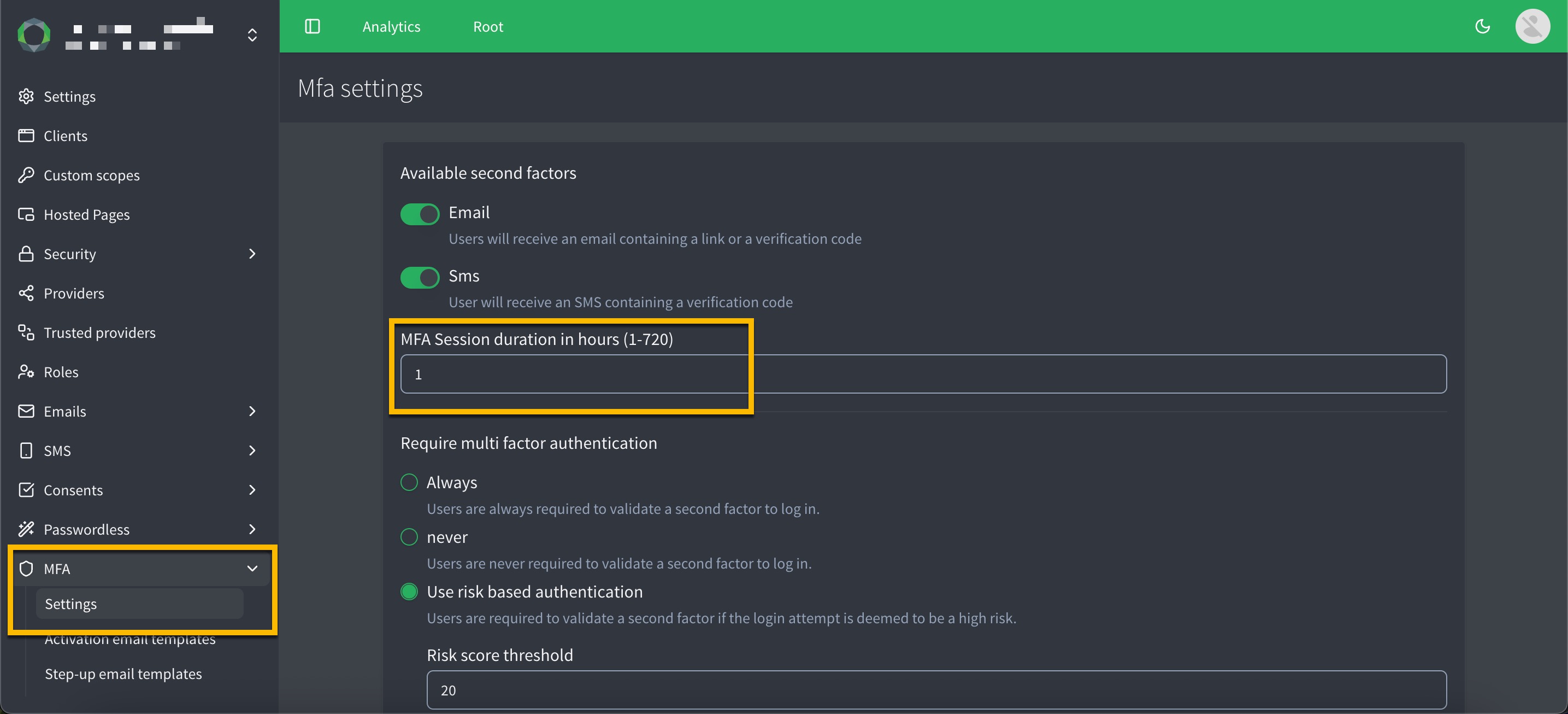
A user who completes MFA on Monday at 09:32 can access MFA-protected features until Thursday at 09:32 (72 hours), even if their SSO session remains active for other tasks. If they perform MFA again within that period (e.g., during a step-up), the MFA validity resets — for example, to Saturday at 17:12 if triggered on Wednesday at 17:12.
This feature helps reduce hijacking risk, supports compliance requirements, and gives you flexibility to balance security with convenience.
For full details, see MFA settings.
iOS SDK 9.1.0
We are pleased to announce the release of the iOS SDK 9.1.0, which includes updates to the logout method.
The logout method now takes parameters for web and native sessions to revoke brower sessions and cookies.
For full details, see our iOS SDK documentation.
Fixes
| Item | Fixed |
|---|---|
In some cases, the OaaS flow wasn’t working as expected with Hosted Pages. |
✓ |
Lite profiles weren’t being properly synced between source and target accounts in our International Consumer Experience feature as expected. |
✓ |
New users were unable to enroll a trusted device if a trusted device cookie already existed. See Risk-based Authentication for more on this topic. |
✓ |